
Curated by our intelligence team, alerts are filtered and ranked by severity for each client. Each alert is mapped to your Intelligence Requirements, contains a description, source, clear actions to be taken and intelligence assessment specific to your organisation.
Book a demo
All of our content is centred around the MITRE ATT&CK® framework. Techniques are tagged so that content can be filtered and visualised according to MITRE techniques. We continuously integrate the latest tactics, techniques and sub-techniques.
Book a demo
ThreatMatch is designed to give you complete control over exactly who you share your intelligence with, how, and when. You can share intelligence with individuals, departments, organisations or within pre-defined trusted groups.
Book a demo
Clients are able to immediately contact analysts to initiate a conversation between the reader and the author of the content. This enables clients and analysts to work collaboratively to receive more highly curated intelligence.
Clients can comment on intelligence, creating an interactive dialogue, both internally, with partners, within trusted groups or with the Security Alliance intelligence team.
Book a demo
Profiles provide you with an in-depth analysis of threat actors, including their usual tactics, techniques and procedures, related tools and malware, incidents and associated profiles. Where appropriate, profiles are mapped against the MITRE ATT&CK framework, including ICS and Mobile matrices. Profiles include:

Attack scenarios provide a comprehensive anatomy of attacks for different threat actors. The scenarios module can be used for mapping and tracking incidents, supporting security testing, security control optimisation and for many other use cases. MITRE ATT&CK® is fully integrated with our own unique and custom-built version of the Navigator.
Book a demo
This module is used for the delivery of regular threat reports, bespoke client reports and research, including links to alerts, incidents, profiles and scenarios. Threat reports are delivered as part of the ThreatMatch subscription.
Book a demo
ThreatMatch provides your team with complete freedom of creation. Create your own intelligence alerts, new threat actor profiles or specific incidents. You choose who you share your content with, internally or within trusted sharing groups or wider communities.
Book a demo
ThreatMatch comes with access to the developer platform, providing API documentation and access to the API endpoints that have been mapped to STIX 2.1 and MISP taxonomies. We also provide a JSON endpoint for an enriched feed, giving you access to all of our content via your preferred security tools.
Book a demo
Communicate with your team and other trusted users through discussion boards. Exchange information around any topic - Alerts, TTPs, Actor Profiles, and more, while keeping everything organised and actionable within ThreatMatch.
Book a demo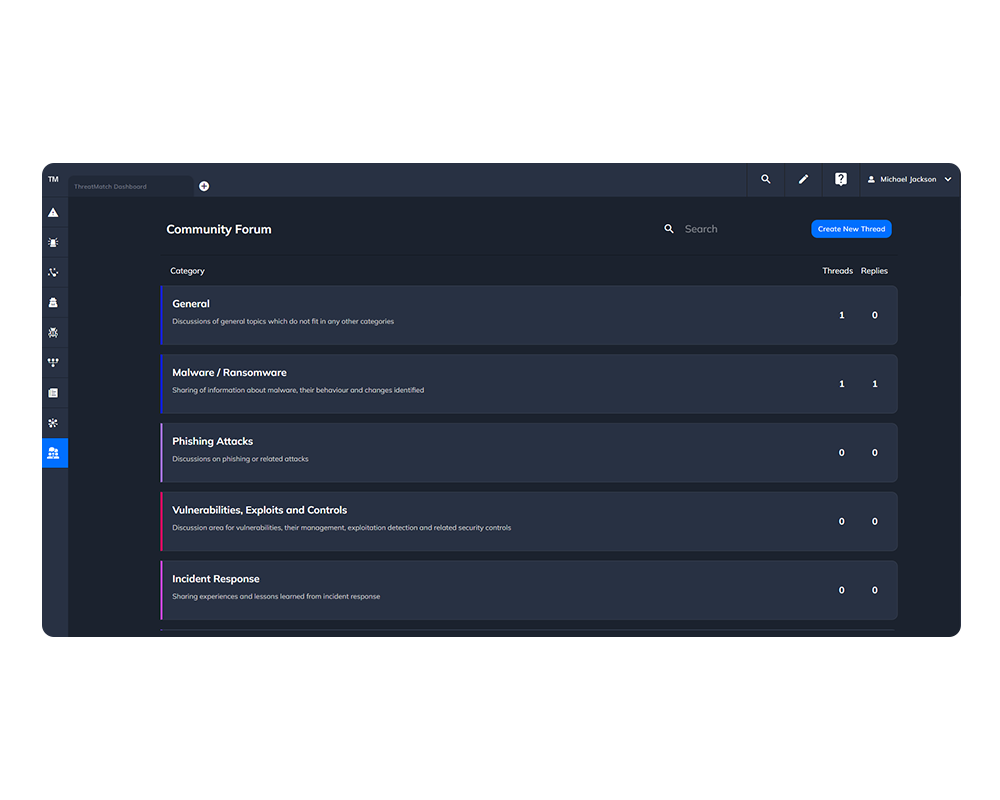
Communicate in real time with analysts or other trusted users directly within ThreatMatch. Whether you're discussing an alert, coordinating an incident, or collaborating on an investigation, Chat provides secure, contextual communication inside the platform.
Book a demo
ThreatMatch enables clients to receive bespoke intelligence for their organisation.

ThreatMatch Community Portal enables the development and operation of secure, trusted communities, based on sector, geography or collaborative efforts.

ThreatMatch Supply Chain Portal includes potential threats to your whole supply chain.

ThreatMatch Conglomerate Portal supports complex organisations to understand threats across all their businesses and operations and share intelligence effectively.

