
In 2026, organisations are drowning in threat data but still struggling to make better cybersecurity decisions. Feeds are richer, telemetry is broader, and alerts are louder than ever. Yet breaches continue to happen not because information is missing, but because true threat intelligence is failing to translate into timely, confident action. The gap between “knowing” and “doing” has never been more consequential.
Threat intelligence has evolved dramatically over the past decade. What began as collections of threat indicators and fragmented threat information has expanded into vast ecosystems of open-source intelligence, commercial intelligence, internal telemetry, and automated analytics. But more data does not automatically mean better intelligence. Without context andvalidation, raw threat data fails to highlight the relevant intelligence that drives decisions.
This is where the definition of good cyber threat intelligence needs a reset. This blog explores what high-quality threat intel actually looks like in 2026: intelligence that is timely, relevant, actionable, and aligned to business risk. By tracing the threat intelligence lifecycle from raw threat data to informed decisions, we aim to help organisations assess their current approach, avoid common pitfalls, and build intelligence capabilities that support proactive, outcome-driven security in an increasingly complex threat landscape.
The threat landscape in 2026 is faster, broader, and more adaptive than ever. Adversaries and threat actors are leveraging AI to automate reconnaissance, personalise social engineering, evade detection, and rapidly modify attack vectors. This has significantly shortened the time between initial access and impact, leaving organisations with far less room to react.
Supply chain risk has also become a constant concern. Modern enterprises depend on complex ecosystems of software, cloud services, and third-party providers, extending risk well beyond the traditional perimeter. A single compromised dependency can now cascade across multiple organisations, making external visibility and operational intelligence essential.
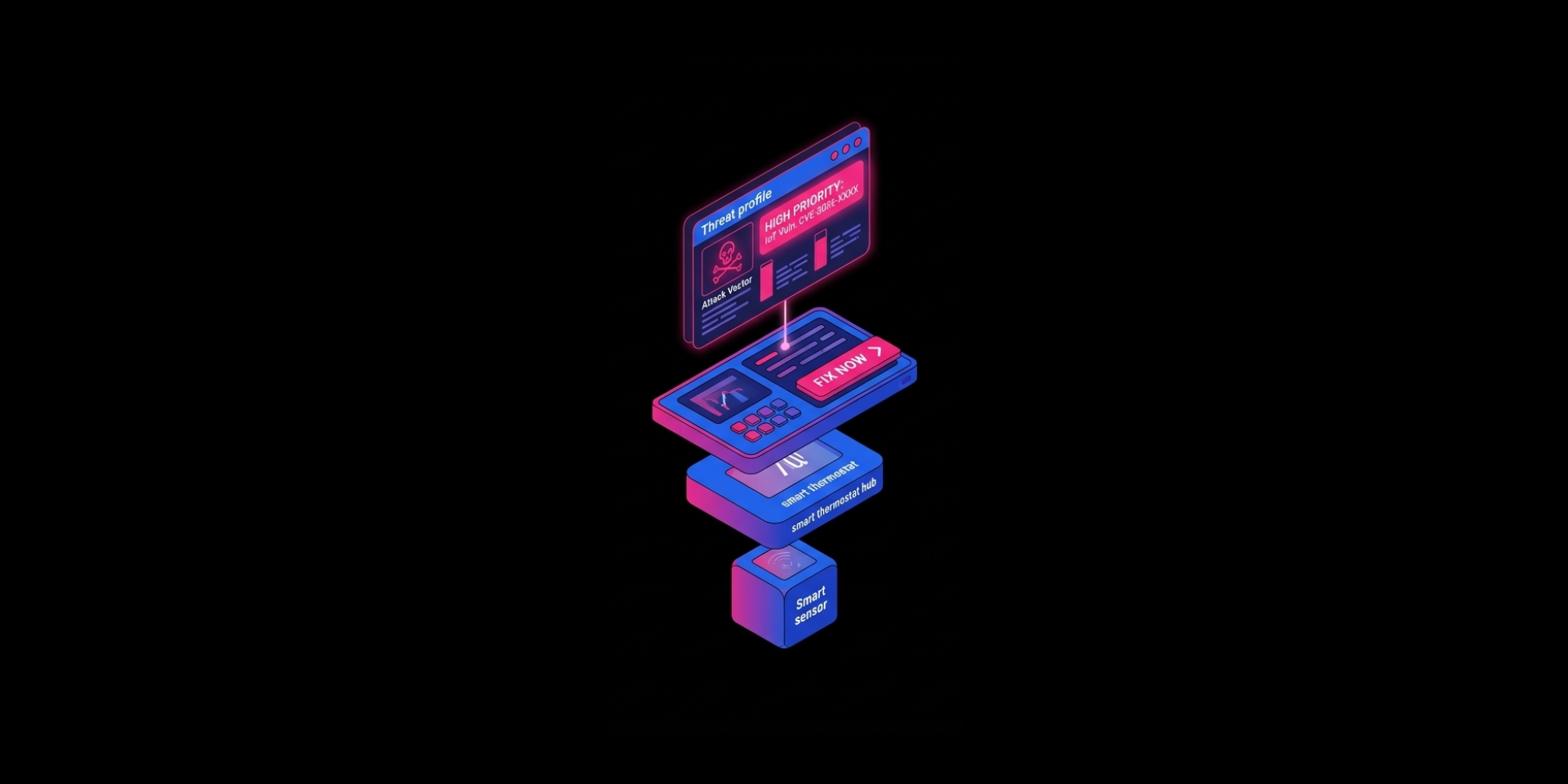
At the same time, the proliferation of IoT and connected operational systems has expanded the attack surface. Many of these devices contain unpatched vulnerabilities and generate limited telemetry, creating persistent blind spots that attackers are increasingly able to exploit, increasing exposure to persistent threats and malware.
Despite this, security professionals are inundated with more threat data than ever before. The sheer volume and sophistication of cyberthreats, often fragmented across tools and teams, makes it difficult to identify potential threats that truly matter. In this environment, traditional, siloed threat intelligence approaches struggle to keep pace, failing to provide the context and prioritisation needed to support timely, risk-informed decisions.
Not all threat intelligence is created equal. In 2026, good threat intelligence is not defined by how much data it contains, but by how effectively it supports decisions. High-quality intelligence shares a few critical attributes:
Understanding these attributes also requires distinguishing between data, information, and intelligence. Raw data consists of unprocessed indicators and signals. Information adds structure and context, such as trends or correlations. Actionable intelligence goes one step further, applying analysis, relevance, and judgement to enable confident, timely decisions aligned to operational risk.
Turning raw threat data into actionable decisions requires a structured process. Organisations that succeed do more than collect information; they contextualise, prioritise, and act on it.
This structured journey transforms overwhelming threat information into intelligence that guides proactive, risk-informed security decisions.
Technology continues to reshape how organisations generate, consume, and act on threat intelligence. In 2026, the right tools can dramatically shorten response times, improve accuracy, and free security teams to focus on higher-value decisions:
In 2026, technology isn’t just an enabler, it’s a force multiplier, allowing intelligence to move from raw threat data to actionable decisions at unprecedented speed.
Even with access to vast amounts of data, organisations often struggle to turn threat intelligence into meaningful action. Some of the most common missteps include:
Avoiding these pitfalls is essential for transforming intelligence into actionable insights that truly support proactive security.
Turning threat intelligence into action requires more than access to data; it demands:
Integrating intelligence into existing workflows ensures that insights flow directly into security operations, incident response, and strategic planning. At the same time, organisations must continuously validate sources and signals, filtering out false positives and outdated information to maintain trust in their intelligence.
Collaboration is also key. Sharing insights with partners, industry groups, and peers enhances visibility into emerging threats, while training teams to interpret and act on intelligence ensures human expertise complements automated systems. Together, these practices create an intelligence capability that is both reliable and actionable.
Looking ahead, strategic intelligence will increasingly shift from reactive reporting to predictive, autonomous, and adaptive approaches. Predictive threat intelligence, autonomous cyber defence, and adaptive risk modelling will enable organisations to anticipate threats and respond automatically to the highest-priority risks.
Security teams will need new skills and mindsets, combining analytical thinking, AI collaboration, and risk-based decision-making. The ultimate goal is to move from responding to incidents toward proactively shaping security strategy, anticipating cyberattacks before they materialise and making informed decisions in real time.

In 2026, good threat intelligence is not defined by the volume of information collected, but by its ability to drive timely, confident action. Intelligence that does not reduce uncertainty, influence decisions, or change outcomes is simply data in disguise.
Organisations that succeed will be those that treat threat intelligence as a living, decision-driven capability, continuously translating raw signals into relevant, prioritised insight aligned to business risk. This requires rethinking not just feeds and platforms, but how intelligence is measured, operationalised, and trusted across the organisation.
In an environment where speed, context, and confidence determine impact, the ability to turn data into decisions is no longer a competitive advantage. It is the baseline for cyber resilience.
Discover how SecAlliance helps organisations transform raw threat data into actionable intelligence that drives faster, risk-informed cybersecurity decisions.